8.3 Server Certificates
For communication between the SMT server and client machines, the encrypted HTTPS protocol is used, requiring a server certificate. If the certificate is not available, or if clients are not configured to use the certificate, the communication between server and clients will fail.
Every client must be able to verify the server certificate by trusting the CA (certificate authority) certificate which signed the server certificate. Therefore, the SMT server provides a copy of the CA at /srv/www/htdocs/smt.crt. This CA can be downloaded from every client via the URL http://FQDN/smt.crt. The copy is created when YaST writes the SMT configuration. Whenever SMT is started with the rcsmt init script, it checks the certificate. If a new CA certificate exists, it is copied again. Therefore, whenever the CA certificate is changed, restart SMT using the rcsmt restart command.
When the SMT Server module applies configuration changes, it checks for the existence of the common server certificate. If the certificate does not exist, YaST asks whether the certificate should be created. If the user confirms, the YaST CA Management module is started.
8.3.1 Certificate Expiration
The common server certificate SMT uses is valid for one year. After that time, a new certificate is needed. Either generate a new certificate using YaST CA Management module or import a new certificate using the YaST Common Server Certificate module. Both options are described in the following sections.
As long as the same CA certificate is used, there is no need to update certificates at the client machines. The generated CA certificate is valid for 10 years.
8.3.2 Creating a New Common Server Certificate
To create a new common server certificate with YaST, proceed as follows:
-
Start YaST and select Security and Users > CA Management. Alternatively, start the YaST CA Management module from a command line by entering yast2 ca_mgm as root.
-
Select the required CA and click Enter CA.
-
Enter the password if entering a CA for the first time. YaST displays the CA key information in the Description tab.
-
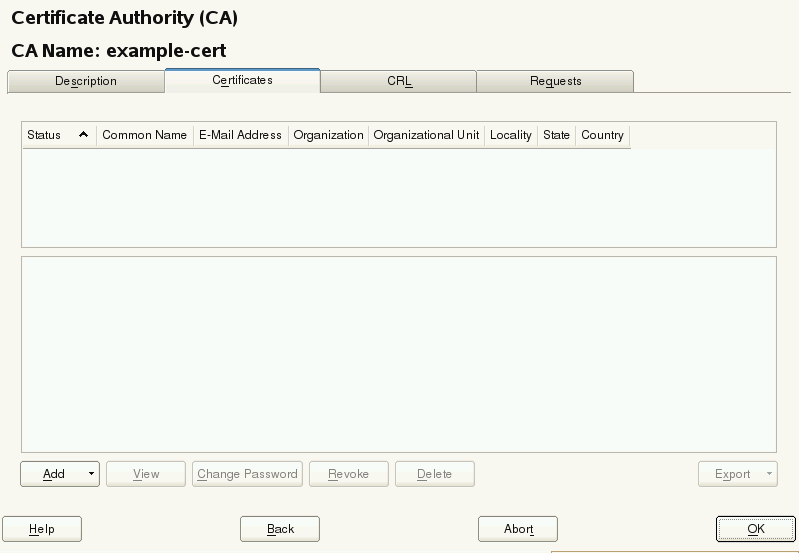
Click the Certificates tab (see Certificates of a CA) and select Add > Add Server Certificate.
Figure 8-1 Certificates of a CA
-
Enter the fully qualified domain name of the server as Common Name. Add a valid e-mail address of the server administrator. Other fields, as Organization, Organizational Unit, Locality, and State are optional. Click Next to proceed.
IMPORTANT: Hostname in Server Certificate
The server certificate must contain the correct hostname. If the client requests server https://some.hostname/, then some.hostname must be part of the certificate. The hostname must either be used as the Common Name, see Step 5, or as the Subject Alternative Name, see Step 7: DNS:some.hostname and IP:<ipaddress>.
-
Enter a Password for the private key of the certificate and reenter it in the next field to verify it.
-
If you want to define a Subject Alternative Name, click Advanced Options, select Subject Alternative Name from the list and click Add.
IMPORTANT: Subject Alternative Name
If Subject Alternative Name is present in the server certificate, than it needs contain the DNS entry. If Subject Alternative Name is present, the Common Name (CN) is not checked anymore.
-
If you want to keep the default values for the other options, like Key Length and Valid Period, click Next. An overview of the certificate to be created is shown.
-
Click Create to generate the certificate.
-
To export the new certificate as the common server certificate, select it in the Certificates tab and select Export > Export as Common Server Certificate.
-
After having created a new certificate, restart SMT using the rcsmt restart command. Restarting SMT ensures that the new certificate is copied from /etc/ssl/certs/YaST-CA.pem to /srv/www/htdocs/smt.crt, the copy SMT uses. Restarting SMT also restarts the Web server.
For detailed information about managing certification and further usage of the YaST CA Management module and the Common Sever Certificate module, refer to the Security Guide coming with the base system.
8.3.3 Importing a Common Server Certificate
You can import an own common server certificate from a file. The certificate to be imported has to be in the PKCS12 format with CA chain. Common server certificates can be imported with the YaST Common Server Certificate module.
To import an own certificate with YaST, proceed as follows:
-
Start YaST and select Security and Users > Common Server Certificate. Alternatively, start the YaST Common Server Certificate module from the command line by entering yast2 common_cert as root.
The description of the currently used common server certificate is shown in the dialog that opens.
-
Click Import and select the file containing the certificate to be imported. Specify the certificate password in the Password field.
-
Press Next. If the certificate is successfully imported, close YaST with Finish.
-
After having created a new certificate, restart SMT using the rcsmt restart command. Restarting SMT ensures that the new certificate is copied from /etc/ssl/certs/YaST-CA.pem to /srv/www/htdocs/smt.crt, the copy SMT uses. Restarting SMT also restarts the Web server.
8.3.4 Synchronizing Time Between SMT Server and Clients
The synchronization of time between the SMT server and clients is highly recommended. Each server certificate has a validity period. If the client happens to be set to a time outside of this period, the certificate validation on the client side fails.
Therefore, it is advisable to keep the time on the server and clients synchronized. You can easily synchronize the time using NTP (network time protocol). Use yast2 ntp-client to configure an NTP client. Find detailed information about NTP in the Administration Guide.